Data Processing Agreement - Current
Data Processing Agreement
Last Revised: July 23, 2025
If you started a subscription before July 23, 2025 your use of the Bringg Services is governed by the terms of the DPA available here.
Table of Contents
- Background
- Definitions
- Roles and Responsibilities
- CCPA
- Processor’s Obligations
- Controller’s Obligations
- Personnel
- Affiliates
- Sub-processing
- International Transfers
- Data Subjects/Consumers Rights
- Personal Data Breach
- Technical and Organizational Measures
- Term
- Miscellaneous
- Exhibit A
- Exhibit B
Background
This Data Processing Agreement (“DPA”) forms part of the Services Agreement by Bringg Delivery Technologies Ltd., and/or any of its Affiliates (“Bringg”) and the Customer entering into the Services Agreement for the subscription to the Services described in the Service Order (the “Customer”). Bringg and the Customer are collectively referred to as the “Parties”, and each a “Party”. All capitalized terms not defined in this DPA shall have the meanings set forth in the Services Agreement.
Unless otherwise expressly stated in the Service Order, this version of the DPA shall be effective and remain in force for the term of such Service Order. In the event of any conflict or inconsistency between the terms of this DPA and the terms of the Service Order, the terms of the Service Order shall control. In the event of any conflict or inconsistency between the terms of this DPA and the terms of the online Terms of Service, the terms of this DPA shall control.
This DPA sets out the roles and obligations that apply when Bringg processes, transfers and gains access to Personal Data on behalf of Customer in the course of providing the Services, and when Bringg, its staff or a third party acting on behalf of Bringg receive access to Personal Data of individuals.
It is agreed that a copy of this DPA may be forwarded to the relevant Supervisory Authority, if required under Applicable Data Protection Legislation. Furthermore, the Parties agree that such authority has the right to conduct an audit of Bringg with respect to the subject matter of this DPA.
1. Definitions
For the purposes of this DPA:
- “Affiliate/s” means any legal entity directly or indirectly controlling, controlled by or under common control with a party to the Services Agreement, where “control” means the ownership of a majority share of the voting stock, equity, or voting interests of such entity;
- “ANPD” means the Brazilian National Data Protection Authority (Autoridade Nacional de Proteção de Dados)
- “Applicable Data Protection Legislation” means all applicable laws and regulations, in each case as may be amended or superseded from time to time, subject to the processing of Personal Data on behalf of the Customer under this DPA, including without limitation (as applicable), (i) the GDPR; (ii) the UK GDPR; (iii) the LGPD; and (iv) the US State Privacy Laws;
- “CCPA” means the California Consumer Privacy Act of 2018, as amended (Cal. Civ. Code §§ 1798.100 to 1798.199), the CCPA Regulations (Cal. Code Regs. tit. 11, §§ 999.300 to 999.337), and any related regulations or guidance provided by the California Attorney General, as amended by the California Privacy Rights Act (“CPRA”);
- “EEA” means the European Economic Area;
- “GDPR” means Regulation 2016/679 of the European Parliament and of the Council on the protection of natural persons with regard to the Processing of Personal Data and on the free movement of such data;
- “IDTA” means the International Data Transfer Addendum to the EU SCC issued by the Information Commissioner’s Office in the UK and effective as of March 21, 2022;
- “LGPD” means the Brazilian Law No. 13.709 of 14 August 2018 which provides for the Protection of Personal Data and amends the Federal Law No. 12.965 of 23 April 2014;
- “Personal Data” means any information relating to an identified or identifiable natural person (data subject), an identifiable natural person is one who can be identified, directly or indirectly, in particular by reference to an identifier such as a name, an identification number, location data, an online identifier or as otherwise referred to as “Personal Information”, “personally identifiable information” or similar term defined in the Applicable Data Protection Legislation;
- “Personal Data Breach” means a breach of security leading to the accidental or unlawful destruction, loss, alteration, unauthorized disclosure of, or access to Personal Data processed, transmitted, stored or otherwise processed;
- “Restricted Transfer” means: (i) where the GDPR applies, a transfer of personal data from the EEA to a country outside of the EEA which is not subject to an adequacy determination by the European Commission; and (ii) where the UK GDPR applies, a transfer of personal data from the United Kingdom to any other country which is not based on adequacy regulations pursuant to Section 17A of the Data Protection Act 2018;
- “Standard Contractual Clauses” or “SCC” means: (i) where the GDPR applies, the contractual clauses annexed to the European Commission’s Implementing Decision 2021/914 of 4 June 2021 on standard contractual clauses for the transfer of personal data to third countries pursuant to the GDPR (“EU SCC“); and (ii) where the UK GDPR applies, standard data protection clauses set out in Decision 2010/87/EC, as amended or replaced from time to time, pursuant to Article 46 of the UK GDPR (“Prior SCC“);
- “Services Agreement” means the Service Order and the online Terms of Service incorporated by reference into the Service Order, and this DPA;
- “UK GDPR” means the Data Protection Act 2018, as well as the GDPR as it forms part of the law of England and Wales, Scotland and Northern Ireland by virtue of section 3 of the European Union (Withdrawal) Act 2018 and as amended by the Data Protection, Privacy and Electronic Communications (Amendments etc.) (EU Exit) Regulations 2019 (SI 2019/419);
- “US State Privacy Laws” means all state laws relating to the protection and processing of personal data in effect in the United States of America, which may include, without limitation, the CCPA as amended by the CPRA, the Virginia Consumer Data Protection Act, the Colorado Privacy Act, the Connecticut Data Privacy Act, and the Utah Consumer Privacy Act;
- The terms recognized by the GDPR, UK GDPR, and LGPD, such as “Controller, “Data Subject”, “Process”, “Processor”, ”Processing”, shall have the meanings set out therein even if such terms are not capitalized in this DPA.
- The terms “Business”, “Service Provider”, “Third Party”, “Personal Information”, “Consumer”, “sell”, “share”, and “Business Purposes” have the meanings given to them in the CCPA.
- The reference to “Supervisory Authority” shall have the meaning set out in the GDPR, and where applicable, shall also refer to the ANPD.
2. Roles and Responsibilities
As between Bringg and Customer, Customer is the Controller of Personal Data for the purposes of the GDPR/UK GDPR/LGPD, and the Business for purposes of the CCPA with respect to the Personal Information that is provided to Bringg for processing under the Services Agreement and as described in Exhibit A; and Bringg shall process the Personal Data and/or Personal Information as a Processor and/or Service Provider, respectively, on behalf of Customer. Each Bringg and Customer may be referred to in this DPA interchangeably as “Processor” or “Bringg”, and as “Customer” or “Controller”.
3. CCPA
- Bringg will process Personal Information in its role as a Service Provider only for the Business Purposes set forth in the Services Agreement, including this DPA. As a Service Provider, Bringg will not sell or share Personal Information or retain, use, or disclose Personal Information (i) for any purpose other than the Business Purpose, including for a commercial purpose other than providing the Services, except as otherwise permitted by the CCPA; or (ii) outside of the direct business relationship between Customer and Bringg.
- Bringg will provide reasonable and timely assistance to assist Customer in complying with its obligations with respect to verifiable Consumer requests as set forth in the Agreement and this DPA;
- Bringg will not combine Personal Information that it receives from, or on behalf of, Customer, with Personal Information that it receives from other sources, except as may be required to perform any Business Purpose (e.g.: combining Personal Information with information received from third-party carriers in connection with the fulfilment of a delivery); and
- Bringg acknowledges and confirms that it does not receive Personal Information as consideration for any Services provided to Customer.
4. Processor’s Obligations
- The Processor, and any person acting under its authority, will collect and process Personal Data under the Services Agreement, only on behalf of the Controller, during the Term and only for the purpose of fulfilling the Services Agreement, under which Bringg will provide the Controller access to its proprietary SaaS-based last-mile logistics and delivery management platform. Processor will carry out the data processing operations, including with regard to transfers of Personal Data to a third country or an international organisation, in accordance with this DPA and any documented instructions received from the Controller (including the instructions of any users accessing the Services on Customer’s behalf).
- The subject matter, nature, purpose and duration of this Processing, as well as the types of Personal Data collected and categories of Data Subjects, are described in Exhibit A to this DPA.
- The Processor will comply with Applicable Data Protection Legislation while processing and using the Personal Data, including by implementing adequate measures to ensure the privacy of the Data Subjects’ Personal Data held by the Processor.
- Other than as permitted under this DPA, the Processor will not: (a) disclose, make available or transfer the Personal Data to any third party; (b) collect, process, retain, disclose or use any Personal Data made available to it for any purposes other than for the performance of the Services Agreement; (c) sell the Personal Information; (d) retain, use, or disclose the Personal Information outside of the direct business relationship between Bringg and the Customer.
- Processor shall keep records of its processing activities in accordance with the Applicable Data Protection Legislation and will grant to Controller and its designees all required information and access rights, strictly in accordance with the Processor’s security policy, in order to demonstrate and verify Processor’s compliance with the Services Agreement, this DPA and with Applicable Data Protection Legislation. The Processor shall allow for and contribute to audits, including inspections, conducted by the Controller or another auditor mandated by the Controller at the Controller’s sole expense. If and to the extent Controller engages third parties to conduct the audit, such third parties have to be bound by confidentiality obligations similar to those agreed by Processor under this DPA. Notwithstanding the above, the Controller shall only be entitled to conduct such inspection during business hours and no more than once during one calendar year, provided that nothing in this section shall limit the timing and scope of any audit required to be conducted by Applicable Data Protection Legislation.
- Controller shall provide the Processor reasonable prior written notice of any audit or inspection to be conducted under this section and shall make (and ensure that each of its auditors makes) reasonable endeavours to avoid causing (or, if it cannot avoid, to minimize) any damage, injury or disruption to the Processors’ premises, equipment, personnel and business while its personnel are on those premises in the course of such audit or inspection.
- Processor will notify Controller without undue delay if Processor is of the opinion that a written instruction received from Controller is in violation of Applicable Data Protection Legislation and/or in violation of contractual duties under the Services Agreement.
- Processor will notify Controller without undue delay if Processor or Processor’s employees violate the provisions of this DPA. Furthermore, if Processor is of the opinion that Personal Data have been or might have been illegally transferred or otherwise illegally disclosed by it to a third party, Processor will notify Controller thereof without undue delay.
- Processor undertakes to use reasonable endeavours to fully cooperate and to comply with any instructions, guidelines and orders received from the relevant Supervisory Authority.
- Where applicable, Processor shall, taking into account the nature of the processing and the information available to the Processor, assist Controller in meeting the Controller’s obligations to Data Subjects pursuant to applicable law, including assistance in helping Data Subjects to exercise their rights under applicable law, by implementing appropriate technical and organisational measures.
- Upon termination of the Services Agreement, Processor will, at the choice of the Controller, delete or return to the Controller, all Personal Data provided by Controller during the provision of the Services, and delete existing copies of such Personal Data which are kept in its systems and/or premises, all unless Personal Data is required to be retained by Processor under Applicable Data Protection Legislation. Return or deletion of the Personal Data may be made by way of an application program interface made available to the Controller. In that case, the Processor warrants that it will guarantee the confidentiality of the Personal Data transferred and will not actively process the Personal Data transferred anymore.
5. Controller’s Obligations
- Controller is responsible for the evaluation of the admissibility of the data processing activities and for ensuring the rights of the Data Subjects concerned.
- Controller shall be entitled to issue written instructions regarding the scope and the procedure of the data processing activities, within the scope of the Services Agreement. Processor may charge applicable fees for such instructions or terminate the Services Agreement if it does not wish to comply with such instructions.
- The Controller warrants and undertakes that: (i) the Personal Data has been collected, processed and transferred in accordance with the Applicable Data Protection Legislation, including if required, the Controller has received all required consents from its Data Subjects; (ii) after assessment of the requirements of the Applicable Data Protection Legislation, the security measures that the Processor implements under this DPA are appropriate to protect the Personal Data against accidental or unlawful destruction or accidental loss, alteration, unauthorised disclosure or access, in particular where the processing involves the transmission of data over a network, and against all other unlawful forms of processing, and that these measures ensure a level of security appropriate to the risks presented by the processing and the nature of the Personal Data to be protected having regard to the state of the art and the cost of their implementation; (iii) it will promptly respond to any inquiries from Data Subjects and the applicable authorities concerning processing of the Personal Data by the Processor; (iv) it will ensure the rights of the Data Subjects concerned, including without limitation will enable the Data Subjects to inspect and correct the Personal Data which is held by the Processor where such Personal Data is inaccurate, incomplete, unclear, outdated, all as required under Applicable Data Protection Legislation; (v) it will not provide Processor any data of Data Subjects under the age of 16; and (vi) the Data Subject has been informed or will be informed before, or as soon as possible after, the transfer, that his/her personal data could be transmitted to a third country, outside of the EEA.
- Controller agrees to defend, indemnify and hold the Processor its officers, directors, employees, agents, vendors and third party providers, harmless against any and all claims, losses, penalties, causes of action, damages, liability, costs, expenses (including but not limited to attorney’s’ fees and costs) or claims caused by or resulting directly or indirectly from: (i) Controller’s breach of any representation, warranty or obligation under this DPA or under Applicable Data Protection Legislation which applies to the Controller; and; (ii) a third party claim, suit or proceeding that use of the Personal Data within the scope of this DPA infringes any privacy right of a third party.
6. Personnel
- It is hereby agreed that Processor may allow its employees to access the Personal Data, all in order to perform Processor’s obligations and duties under the Services Agreement.
- Processor will be responsible for using qualified personnel with data protection training to provide the data processing activities.
- Processor will ensure that its personnel authorised to process the Personal Data on its behalf, will keep confidential and will not make available any Personal Data received in connection with the Services Agreement to any third party.
7. Affiliates
- Some of Processor’s obligations may be performed by Processor’s Affiliates, as detailed in the Sub-processor’s list available here. Controller acknowledges that Processor’s Affiliates may Process Personal Data on Processor’s behalf to perform the Services under the Services Agreement.
- Processor will be liable for the acts and omissions of its Affiliates to the same extent Processor would be liable if performing the Services under the Services Agreement.
- Controller hereby consents to Processor’s use of Processor’s Affiliates in the performance of the Services in accordance with the terms of this Section 7.
8. Sub-processing
- The Controller hereby grants the Processor a general authorization to use the sub-processors (“Sub-Processors”) listed here (“Sub-Processors List”) to process Personal Data and/or Personal Information on Bringg’s behalf for the purpose of providing the Services under the Services Agreement. All such Sub-processors shall be Service Providers for purposes of the CCPA.
- Processor will maintain the Sub-processors List up to date and will update it in case of any change of the Sub-Processors and shall notify Customer at least seven (7) days prior to any such change. Processor shall: (i) communicate the name, address and contact details of the Sub-Processor and the tasks of the Sub-Processor, (ii) ensure that it has in place or conclude prior to engaging the Sub-Processor a sub-processing agreement between Processor and the Sub-Processor that is no less protective with respect to Controller’s interest and protection of Personal Data than required by Applicable Data Protection Legislation, and in particular providing sufficient guarantees to implement appropriate technical and organisational measures, (iii) ensure that an adequate level of data protection for Sub-Processors that are located outside of the EEA exists or is created (e.g. by concluding Standard Contractual Clauses), (iv) ensure that it has sufficient rights against the Sub-Processor to enforce a claim or request of Controller in context of the Services provided by the Sub-Processor; and (v) upon Customer’s request, provide the copies of the Sub-Processor agreements pursuant to Clause 9(c) of the EU SCCs in a manner to be determined in Bringg’s discretion and with all commercial information, or clauses unrelated to the EU SCCs or their equivalent, removed by Bringg beforehand.
- Objection to Sub-Processors. Customer may object prior to Bringg’s appointment or replacement of a Sub-Processor, provided such objection is based on reasonable grounds relating to data protection. In such event, the Parties shall cooperate in good faith to reach a resolution and if such resolution cannot be reached, then Bringg, at its discretion, will either not appoint or replace the Sub-Processor or, will permit Customer to suspend or terminate the affected Services (without prejudice to any fees incurred by Customer prior to suspension or termination).
9. International Transfers
- The Parties agree that when the Processing of Personal Data by Bringg includes a Restricted Transfer (either directly or via onward transfer), it shall be subject to the appropriate Standard Contractual Clauses as follows:
- in relation to Personal Data that is protected by the GDPR, Module Two of the EU SCCs will apply where Customer is directly engaged in a Restricted Transfer, and Module Three of the EU SCCs will apply where Bringg is engaged in a Restricted Transfer on behalf of the Customer, and the Parties elect as follows: (i) include optional Clause 7; (ii) in Clause 9(a), Option 2 will apply, and the time period for prior notice of Sub-processor changes shall be as set out in Section 7.2 of this DPA; (iii) in Clause 11, the optional language will not apply; (iv) in Clause 17, Option 1 will apply, and the EU SCCs will be governed by Irish law; (v) in Clause 18(b), disputes shall be resolved before the courts of Ireland; (vi) Annex I of the EU SCCs shall be deemed completed with the information set out in Exhibit A to this DPA; (vii) Annex II of the EU SCCs shall be deemed completed with the information set out in Exhibit B to this Agreement; and
- in relation to Personal Data that is protected by the UK GDPR, for so long as it is lawfully permitted to rely on Prior SCC for transfers of Personal Data from the United Kingdom, the Prior SCC shall apply on the following basis: (i) Appendix 1 shall be completed with the relevant information set out in Exhibit A to this DPA; (ii) Appendix 2 shall be completed with the relevant information set out in Exhibit B to this DPA; (iii) the optional illustrative indemnification Clause will not apply, references in the Prior SCC to “the law of the Member State in which the data exporter is established” shall be deemed to mean “the laws of England and Wales”; and (iv) any other obligation in the Prior SCCs determined by the Member State in which the data exporter is established shall be deemed to refer to an obligation under UK GDPR.
- Where the Prior SCCs do not apply and the Parties are lawfully permitted to rely on the EU SCC for Restricted Transfers of Personal Data via the Services from the UK, either directly or via onward transfer, subject to completion of the IDTA, then the EU SCC, completed as set out above in Section 9.1(a) of this DPA shall also apply to transfers of such Personal Data, subject to the provision that the IDTA shall be deemed executed between Bringg and Customer, and the EU SCC shall be deemed amended as specified by the IDTA in respect of the transfer of such Personal Data.
- If neither sub-section (b) or sub-section (c) applies, then Customer and Bringg shall cooperate in good faith to implement appropriate safeguards for transfers of such Personal Data as required or permitted by the UK GDPR without undue delay.
- In the event that any provision of this DPA contradicts, directly or indirectly, the Standard Contractual Clauses, the Standard Contractual Clauses shall prevail.
10. Data Subjects/Consumers Rights
- Processor shall, to the extent legally permitted, promptly notify Controller if it receives a request from a Data Subject to exercise the Data Subject’s right of access, right to know, right to rectification, restriction of processing, erasure, data portability, or to object to processing, each a “Data Subject Request” or a “Consumer Request” (with respect to the applicable US State Privacy Laws). Processor will not respond to any such requests unless authorized to do so by Controller or as required under Applicable Data Protection Legislation or under the instructions of a Supervisory Authority.
- For the purpose of the CCPA, the Service Provider shall not be required to comply with a verifiable Consumer Request received directly from a Consumer. The Service Provider will provide assistance to the Business with respect to the Business’ response to a verifiable Consumer Request, including, by providing to the Business the Consumer’s Personal Information in the Service Provider’s possession, which the Service Provider obtained as a result of providing Services to the Business, and through appropriate technical and organizational measures, taking into account the nature of the processing.
- Processor shall provide commercial reasonable assistance to Controller by taking appropriate technical and organisational measures for the fulfilment of Controller’s obligation to respond to requests for exercising the Data Subjects’ rights as laid down by Applicable Data Protection Legislation. Unless prohibited under the Applicable Data Protection Legislation, Controller will reimburse Processor with any costs and expenses related to Processor’s provision of such assistance.
11. Personal Data Breach
The Processor shall notify the Controller without undue delay after becoming aware of a Personal Data Breach and take necessary and reasonable action to remediate such violation. Additionally, Bringg shall, taking into account the nature of the Processing and the information available to Bringg, provide Customer with reasonable cooperation and assistance necessary for Customer to comply with its statutory obligations under the Applicable Data Protection Legislation. Each party will reasonably assist the other party to mitigate any potential damages in connection with this Section 11.
12. Technical and Organizational Measures
Processor will implement the technical and organizational security measures as stipulated in Exhibit B of this DPA and as further detailed at: https://security.bringg.com/. The technical and organizational security measures are aimed at protecting Personal Data against accidental or unlawful destruction or accidental loss, alteration, unauthorized disclosure or access and against all other unlawful forms of processing.
13. Term
This DPA shall become effective upon the effective date of the Services Agreement that expressly incorporates the terms of this DPA by reference. This DPA shall remain in full force until the Services Agreement terminates (the “Term“).In the event that the Processor is in breach of its obligations under this DPA, then the Controller may temporarily suspend the transfer of Personal Data to the Processor until the breach is repaired or the DPA is terminated.
14. Miscellaneous
Each Party’s and all of its Affiliates’ liability, taken together in the aggregate, arising out of or related to this DPA, whether in contract, tort or under any other theory of liability, is subject to the applicable limitation of liability section of the Services Agreement, and any reference in such section to the liability of a party means the aggregate liability of that Party and all of its Affiliates under the Services Agreement and this DPA together. This DPA represents the complete agreement concerning the subject matter hereof. The Parties may amend this DPA, from time to time by mutual agreement of both Parties, and subject to compliance with any required obligations under Applicable Data Protection Legislation (i.e., to inform the applicable authority where required). This DPA shall be governed by and construed under the laws stipulated in the Services Agreement, without reference to principles and laws relating to the conflict of laws. The competent courts of the law stipulated in the Services Agreement shall have the exclusive jurisdiction with respect to any dispute and action arising under or in relation to this DPA. If Processor makes a material change to this DPA, which it may do from time to time, then Processor will post the updated DPA to its website. Controller is responsible for checking for any change to this DPA. Continued use of the Services after a change has been posted constitutes Controller’s acceptance of any new or modified DPA.
Exhibit A
Details of Processing
This Exhibit A forms part of the DPA and describes the processing that Bringg will perform on behalf of the Customer.
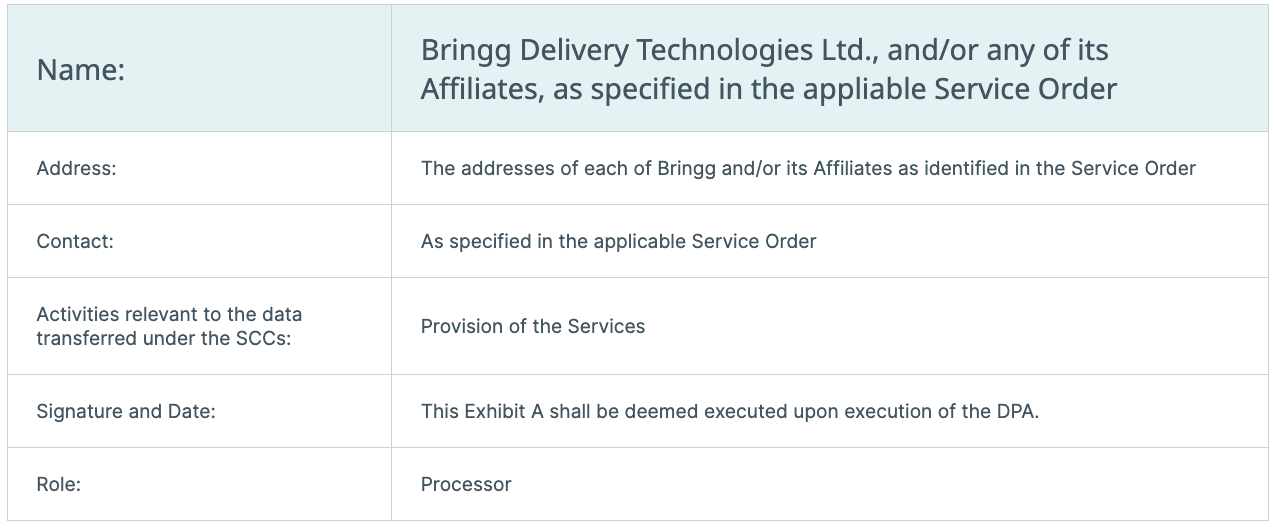
The Parties
1. Controller/ Data exporter
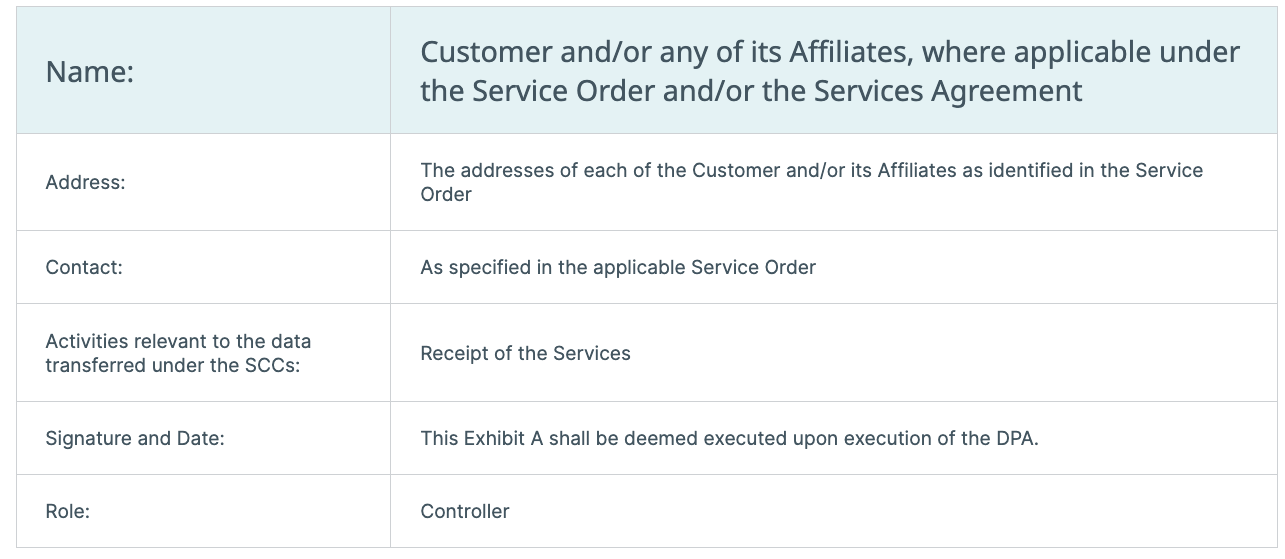
Processor/Data importer
2. Subject Matter of the Processing:
The Personal Data is collected and processed by Processor when Controller gains access to Processor’s proprietary SaaS-based last-mile logistics and delivery management platform, the driver mobile application (“Bringg Delivery Management Platform”), and the Zenkraft offering.
3. Duration of Processing:
Term of the applicable Service Order.
4. Nature of Processing:
Provision of the Services (including support).
5. Categories of Data Subjects:
Controller’s internal and/or external Mobile Personnel, End Customers, Admins, Dispatchers, Users and/or any other individuals whose Personal Data is provided by the Controller to Processor
6. Categories of Personal Data:
- Product: Bringg Delivery Management Platform
- Category of Data: any information provided by the Controller to Processor, which may include End-Customer’s name, telephone number, address, e-mail address, list of delivered goods, location, and other information required to process a shipment, fulfil an order until its delivery, or process a return, and any other data Customer or a carrier requires to add to the labels on the delivered goods; Mobile Personnel’s name, phone number, locations, and email address, IP/MAC address, photo (optional), voice & video recording (optional), ID copy/driver license copy for the purpose of age verification for specific deliveries (optional). For detailed information please visit the “Solution” page.
- Product: Zenkraft
- Category of Data: any information provided by the Controller to Processor, which may include such End-Customer’s name, telephone number, address, e-mail address, list of delivered goods, location, IP address, and other information required to process a shipment, fulfill an order until its delivery, or process a return, and any other data Customer or a carrier requires to add to the labels on the delivered goods.
7. Sensitive or Special Categories of Personal Data:
None. Processor does not intentionally collect and Controller is not required to transfer any sensitive Personal Data in relation to the Data Subjects. If Controller’s Users (Dispatchers) and Mobile Personnel choose to use the chat functionality of the Services, they may (but do not have to) exchange voice & video recordings which may qualify as sensitive Personal Data. In addition, if Controller instructs Processor, at Controller’s option, to request an identification card for the purpose of age verification in connection with delivery of specific goods (e.g.: alcohol), Processor may request such data through the Services (‘opt-in’).
8. To the extent the Module Two or Module Three of the EU SCCs applies to this DPA:
- Frequency of the transfer: Continuous, as required for the Services.
- Personal Data Retention Period:Processor will retain Personal Data it processes hereunder only for as long as required to provide the Services pursuant to the Services Agreement. Unless otherwise agreed in writing by the Parties, after a request from the Controller to delete any Personal Data or upon termination or expiration of the Services Agreement, an automated process will begin that permanently deletes the data in accordance with the timelines set forth in the tables below.
- For transfers to the Subprocessors, subject matter, nature and duration of the Processing: Refer to Section 8 of the DPA.
- Competent Supervisory Authority: The Supervisory Authority competent under Clause 13(a) of such EU SCCs shall be the Irish Data Protection Commission.
Bringg Delivery Management Platform

Zenkraft
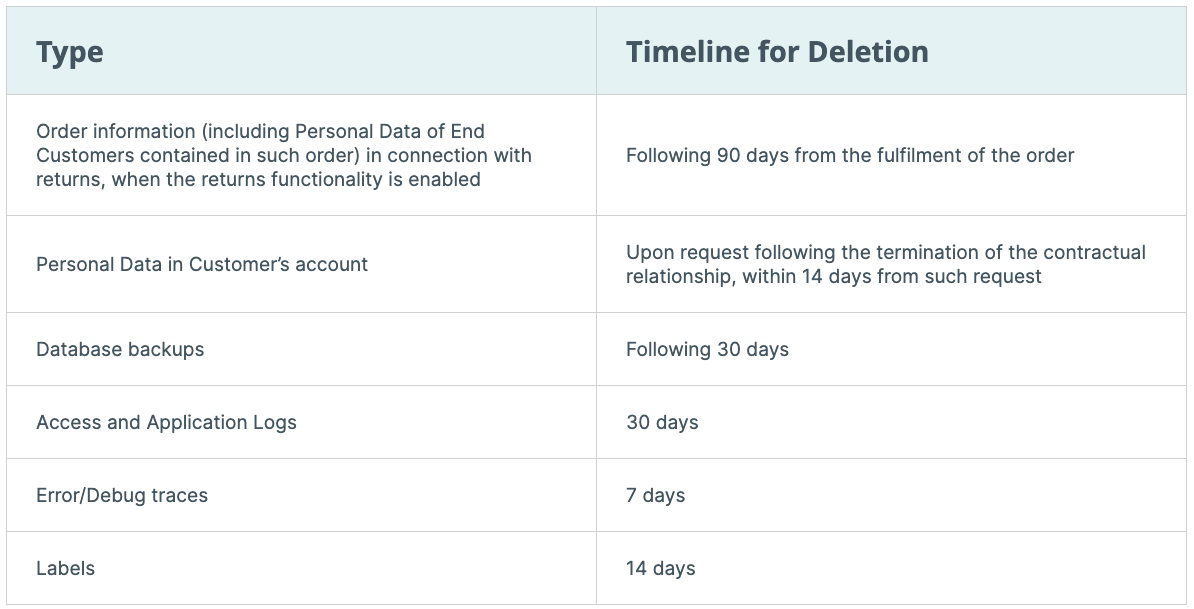
EXHIBIT B
TECHNICAL AND ORGANIZATIONAL SECURITY MEASURES
In order to protect the confidentiality, integrity, and availability of the information and data shared with us by our users and customers and their end-users and customers (collectively “Users”, or “you”), Bringg Delivery Technologies Ltd. and its affiliates (“Bringg”, “us” or “we”) has implemented an information security program that includes technical, administrative/organizational, and physical controls.
Bringg utilizes advanced tools, security procedures and engineering practices to store in a secure fashion, and protect against accidental or unlawful destruction or loss, or unauthorized disclosure or access, all User confidential or sensitive information (“User Information”) that is collected by us as part of the operation of the services of our websites and mobile applications (the “Services”).
Bringg implements a cloud-based SaaS model, currently with the use of the cloud solutions offered by Google Cloud Platform (“GCP”) and for the Zenkraft offering where we integrate with carriers through various Salesforce clouds. All User Information collected by us as part of the operation of the Services is stored and hosted on compute resources provided by GCP and controlled by us (the “Database”). By using GCP we are able to leverage the high performance, durability, scalability, availability and security of the GCP infrastructures and procedures in the provision of our Services.
Our security procedures and practices are implemented in accordance with all applicable data protection laws, are appropriate to the nature of the information collected and are aligned with industry best practices for the management, use, transport, and storage of User Information.
Without limiting the foregoing, we ensure that the following systems and procedures are in place:
1. Security Organization and Program:
- The framework for the Information Security Program includes administrative, organizational, technical, and physical safeguards reasonably designed to protect the Services and confidentiality, integrity, and availability of Customer Data. The Information Security Program is intended to be appropriate to the nature of the Services and the size and complexity of Bringg’s business operations.
- Bringg has a separate and dedicated Information Security team that manages the Information Security Program. Bringg’s security framework is aligned to information security established industry standards.
- Bringg maintains a risk-based assessment security program used to evaluate risks throughout the company on an ongoing basis. The risk management process incorporates management’s risk tolerance, and evaluations of new or evolving risks.
2. Security Certifications and Attestations
- Bringg holds the following security-related certifications and attestations:
- SOC 2 Type II
- ISO 27001
- At least annually, Bringg will engage with an independent assessor to conduct a compliance assessment and provide a full certification, attestation, review, or report. The results of such assessments are available (under NDA) to Customers. To the extent Bringg decides to discontinue a certification or attestation, Bringg will adopt or maintain an equivalent, industry-recognized framework.
3. Business Continuity
- Bringg leverages specialized tools to monitor server performance, data, and traffic load capacity. Bringg is promptly notified in the event of any suboptimal server performance or overloaded capacity.
- Such infrastructure is designed to tolerate system or hardware failures with minimal User impact.
- Bringg publishes system status information on the designated status page.
4. Network Security
- The Production environment is protected by effective network security, to control both inbound and outbound data transport, including proper monitoring of Bringg’s network components to detect unauthorized access.
- The Production environment is protected by cloud service network controls, including firewall and other boundary tools, in order to monitor and control communications at the external boundary of the network and at key internal boundaries within the network. These boundary devices employ rule sets, access control lists, and configurations to enforce the flow of User Information to or from the Production environment.
- All network access between production services is restricted, using access control lists to allow only authorized services to interact in the production network. Access control lists are in use to manage network segregation between different security zones in the production environment.
- Access to the Production environment may only be made through a limited number of access points or through zero-trust solutions, to restrict the access to specific internal services. All communication sessions with the Production environment are encrypted.
- All User Information transmitted to or from the Production environment is encrypted.
5. Monitoring
- The network on which User Information is transmitted to or from the Production environment is constantly monitored by a wide variety of automated monitoring systems, which are designed to detect unusual or unauthorized activities and conditions at communication points.
- These tools monitor server and network usage, port scanning activities, application usage, and unauthorized intrusion attempts and set custom performance metrics thresholds for unusual activity.
6. Penetration Testing
- Bringg performs penetration tests and engages independent third-party entities to conduct application Mobile and API penetration tests on at least an annual basis.
- Security threats and vulnerabilities that are detected are prioritized, triaged, and remediated promptly.
7. Security Incident Management
- Bringg maintains security incident management policies and procedures. Bringg’s Incident Response Team assesses all relevant security threats and vulnerabilities and establishes appropriate remediation and mitigation actions.
- Bringg notifies impacted Customers without undue delay of any unauthorized disclosure of Customer Data related to their respective customers.
8. Confidentiality
- Bringg has controls in place to maintain the confidentiality of Customer Data.
- All Bringg’s employees and contractors are bound by Bringg’s internal policies regarding maintaining the confidentiality of Customer Data and are contractually obligated to comply with these obligations.
9. Hosting Architecture and Data Segregation
- The production environment within GCP where the Services and Customer Data are hosted are logically isolated in a Virtual Private Cloud (VPC). Customer Data stored within GCP is encrypted at all times. GCP does not have access to unencrypted Customer Data.
- More information about GCP security is available at https://cloud.google.com/security/. For GCP compliance audits and reports, please see https://cloud.google.com/security/compliance/.
10. Physical Security
- GCP strictly controls both at the perimeter and at building ingress points by professional security staff utilizing video surveillance, intrusion detection systems, and other electronic means. Authorized staff must pass two-factor authentication (2FA) a minimum of two (2) times to access data center floors. All visitors and contractors are required to present identification and are signed in and continually escorted by authorized staff. These facilities are designed to withstand adverse weather and other reasonably predictable natural conditions. Each data center has redundant electrical power systems that are available twenty-four (24) hours a day, seven (7) days a week. Uninterruptible power supplies and on-site generators are available to provide back-up power in the event of an electrical failure. More information about GCP data center security is available at https://www.google.com/about/datacenters/data-security/.
- In addition, Bringg headquarters and office spaces have a physical security program that manages visitors, building entrances, closed circuit televisions, and overall office security.
11. Security by Design
- Bringg follows security by design principles when it designs the Services.
- Bringg also applies a Secure Software Development Lifecycle (Secure SDLC) standard to perform numerous security-related activities for the Services across different phases of the product creation lifecycle from requirements gathering and product design all the way through product deployment. These activities include, but are not limited to, the performance of (a) internal security reviews before deploying new Services or code; (b) penetration testing by independent third-parties; and/or (c) threat models for new Services to detect potential security threats and vulnerabilities.
12. Access Controls
- Provisioning Access – To minimize the risk of data exposure, Bringg follows the principles of least privilege through a team-based-access-control model when provisioning system access. Bringg personnel are authorized to access Customer Data based on their job function, role, and responsibilities. Access rights to production environments are reviewed at least annually. An employee’s access to Customer Data is promptly removed upon termination of their employment. In order to access the production environment, an authorized user must have unique credentials with multi-factor authentication enabled.
- Password Controls – Bringg’s current policy for employee password management follows the NIST 800-63B guidance, and as such, our policy is to use longer passwords, with multi-factor authentication, but not frequent changes. When a customer logs into its account, Bringg hashes the credentials of the user before it is stored.
13. Change Management
- Bringg has a formal change management process it follows to administer changes to the production environment, including any changes to its underlying software, applications, and systems. Each change is reviewed and evaluated in a test environment before being deployed into the production environment. All changes, including the evaluation of the changes in a test environment, are documented using a formal, auditable system of record.
14. Encryption
- The databases that store Customer Data are encrypted using the Advanced Encryption Standard
- All communication (including customer Data) transit between the end user and the production environment is encrypted using TLS.
15. Customer Data Backups
- Bringg performs regular backups of Customer Data, which is hosted on GCP data center infrastructure. Customer Data that is backed up is retained redundantly across multiple availability zones and encrypted in transit and at rest using the Advanced Encryption Standard.
16. Organizational Security
- We implement a security awareness program to train Bringg personnel about their security obligations.
- We have clearly defined roles and responsibilities for our personnel. We conduct appropriate screening before hiring any personnel who may have access to the Database or User Information.